This tale was initially posted and last up to date .
Android may perhaps have begun with the mantra that developers are allowed to do just about anything as long as they can code it, but items have transformed more than the years as protection and privacy grew to become bigger priorities. Every single main update in excess of the last 10 years has shuttered functions or extra restrictions in the name of safeguarding consumers, but some sacrifices may perhaps not have been completely necessary. An additional Android 11 trade-off has emerged, this time getting away the ability for customers to find third-occasion digicam applications to choose pics or videos on behalf of other applications, forcing people to rely only on the created-in digital camera application.
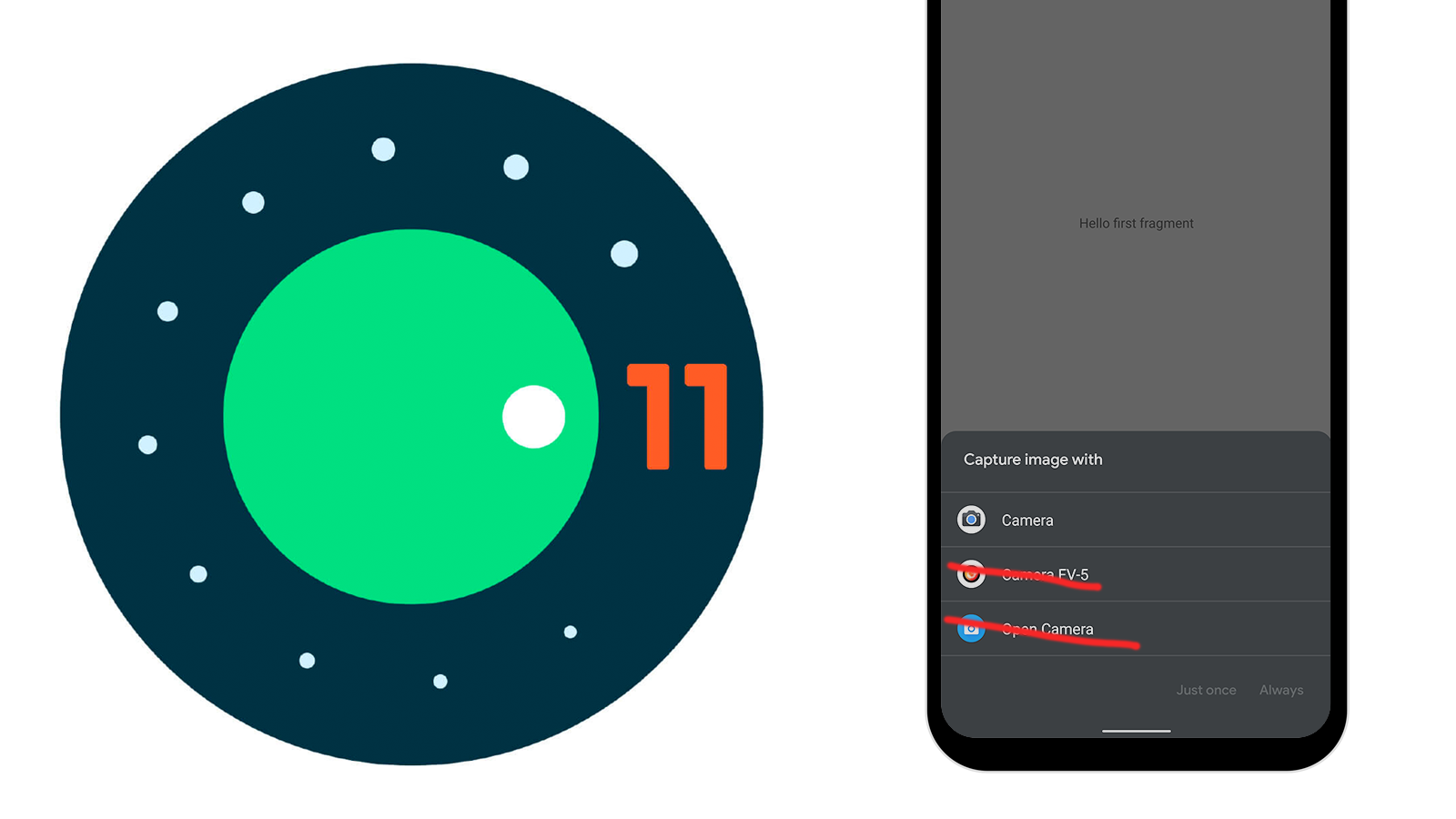
At the heart of this modify is 1 of the defining attributes of Android: the Intent process. Let’s say you have to have to acquire a picture of a novelty coffee mug to provide by means of an auction application. Since the auction application was not created for photography, the developer selected to leave that up to a appropriate camera application. This wherever the Intent program comes into participate in. Builders just develop a ask for with a couple of standards and Android will prompt end users to decide from a list of put in apps to do the occupation.
Digicam picker on Android 10.
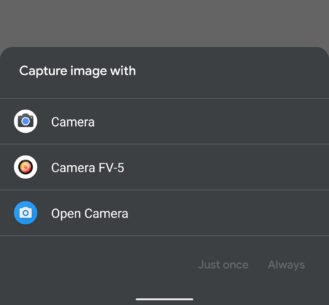
Even so, matters are likely to transform with Android 11 for apps that inquire for shots or movies. Three precise intents will cease to do the job like they utilised to, which include: Online video_Capture, Image_Capture, and Impression_Capture_Secure. Android 11 will now instantly provide the pre-put in digicam app to perform these steps without the need of ever exploring for other apps to fill the role.
Beginning in Android 11, only pre-mounted method camera apps can answer to the subsequent intent steps:
If a lot more than one particular pre-mounted system digicam application is readily available, the program provides a dialog for the user to pick an app. If you want your app to use a certain 3rd-get together camera app to capture pictures or video clips on its behalf, you can make these intents explicit by environment a bundle identify or part for the intent.
Google describes the modify in a listing of new behaviors in Android 11, and even further confirmed it in the Concern Tracker. Privacy and protection are cited as the cause, but there is certainly no dialogue about what accurately made those people intents unsafe. Perhaps some end users were tricked into location a malicious camera app as the default and then utilizing it to capture things that ought to have remained personal.
“… we imagine it is the suitable trade-off to defend the privateness and stability of our customers.” — Google Problem Tracker.
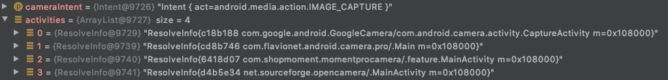
Not only does Android 11 take the liberty of quickly launching the pre-mounted digicam application when requested, it also prevents app developers from conveniently furnishing their have interface to simulate the very same operation. I ran a check with some straightforward code to query for the digicam apps on a cellphone, then ran it on equipment working Android 10 and 11 with the exact established of digital camera applications put in. Android 10 gave back a total set of applications, but Android 11 reported very little, not even Google’s very own pre-mounted Digital camera application.
Over: Debugger look at on Android 10. Beneath: Similar look at on Android 11.
As Mark Murphy of CommonsWare details out, Google does prescribe a workaround for developers, despite the fact that it truly is not incredibly beneficial. The documentation advises explicitly examining for set up digital camera applications by their package deal names — which means developers would have to choose preferred apps up entrance — and sending end users to people apps immediately. Of course, there are other means to get solutions without the need of pinpointing all bundle names, like finding a listing of all applications and then manually exploring for intent filters, but this appears like an over-complication.
The new habits is enforced in at the very least the existing Android 11 beta release, and it will happen to any apps no matter of no matter if they target API 30 or a little something reduced. We will not know but if the Android CTS (Compatibility Exam Suite) will require this conduct or if OEMs will be authorized to improve it again to the earlier policies, but it truly is probably this will turn out to be the normal heading ahead.
This unquestionably isn’t a devastating improve, and for quite a few end users that previously default to their created-in digital camera, it will be totally clear. And most apps will even now permit consumers to switch around to their desired digicam to seize a great shot, then add it from the gallery. Nonetheless, this indicates far more function for buyers, and it’s a kick in the pants to people that often snap profile pictures with a filter or for these that count on G Cam ports to swap their stock camera. In addition, some applications you should not allow for for unique workflows, which means you are caught with no matter what digital camera app is there.
Google attributes the adjust to prospective geotag hijacking
In a response to The Verge, Google defined that this modify was manufactured to “preserve bad actors from probably harvesting your locale.” This clarification was also added in an update to the list of improvements in Android 11, together with much more specialized facts and a clarification that this does not inhibit the capability to set up and use third-occasion digicam apps.
This is developed to assure that the EXIF site metadata is effectively processed dependent on the spot permissions described in just the app sending the intent.
To get EXIF locale metadata from the pre-set up procedure digital camera app when utilizing intents that have one of the preceding intent steps, your application should declare
Access_MEDIA_Sitein addition to theObtain_COARSE_AreaorAccess_High-quality_Areapermission.If you want a precise 3rd-occasion digital camera app to cope with your app’s intent, you might do so by explicitly specifying the 3rd-party digicam app’s package deal name to satisfy the intent.
This adjust does not affect users’ capability to put in and use any digital camera application to capture images or videos directly. A consumer can established a third occasion digicam app as the default digicam application. This modify also isn’t going to influence intent actions that launch the person-specified default camera app, including
android.supplier.MediaStore.INTENT_Motion_Nevertheless_Image_Digital camera,android.service provider.MediaStore.INTENT_Motion_Nonetheless_Impression_Digital camera_Safe, orandroid.company.MediaStore.INTENT_Action_Movie_Digicam.
Harvesting EXIF info in this way has basically been documented in the previous when Shutterfly was caught performing it in 2019. This modify will prohibit the least difficult path to hijacking site knowledge, but it leaves some workarounds like calling out to digicam applications directly or asking consumers to acquire shots and load them from a media service provider. It is really probable Google may well have to choose more methods to absolutely shut the doorway on this tactic.

Problem solver. Incurable bacon specialist. Falls down a lot. Coffee maven. Communicator.