According to Scolar, an enterprise’s enterprise’s provider of cloud information security services for enterprises, there has been a huge increase in attacks among ongoing infectious diseases on the Internet of Things (IoT) devices.
During the two weeks of last December, there were approximately 300,000 infiltration attempts using malicious software for IoT platforms. This is eight times or 700% more than the Zscaler systems recorded before the onset of Pandemic.
Almost all IoT malware belongs to the Gaffit and Mirai families. About 60% of attacks originate in China. The United States and India are in the rankings of countries of origin. Ireland (48%), the United States (32%) and China (14%) were the worst hit.
The most targeted targets of cybercriminals are currently all types of decoders (29%), smart TVs (20%) and smart watches (15%). Among the IoT devices often ignored by IT departments, researchers found cars, “smart” refrigerators, and Wi-Fi enabled memory cards – all of which go online and access cloud resources.
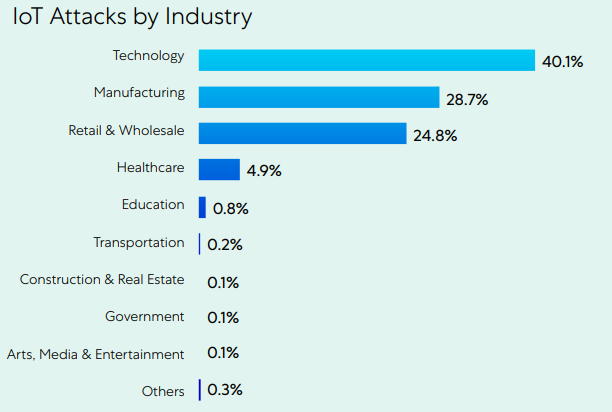
However, in most cases the victims of the attack are companies in the manufacturing, commercial and healthcare sectors. At the same time, corporate tools in the first two areas proved to be the most “sustainable heart.” Worst of all, even in healthcare, data exchange is only protected in half the cases, however, as the study authors point out, all 553 devices identified support traffic encryption.

Tv fanatic. Amateur food maven. Devoted webaholic. Travel lover. Entrepreneur. Evil writer. Beer guru.